Introduction
Enterprise risk management (ERM) is an essential practice in businesses that are enthusiastic about dealing with uncertainties and their impacts on the realization of organizational goals. It allows companies to direct their effort to the most relevant risks that may hinder the achievement of corporate objectives. The future performance of an organization is inextricably connected to the degree of risk that it can tolerate. Aven (2013) defines risk as “an uncertain future outcome that can either improve or worsen a company’s position” (p. 463). The level of risk that an institution takes both deliberately or involuntarily determines if the future results boost or ruin the position of the organization. Hence, risk acceptance and risk appetite are essential ingredients of a successful ERM program. According to Aven (2013), risk appetite refers to “the amount of threat exposure or potential adverse impact from an event that an organization is willing to accept” (p. 465). This article will discuss the strategies that organizations can use to determine risk appetite and conduct a hazard assessment.
Determining Risk Appetite
The determination of risk appetite is significant because it enables organizations to exploit emerging opportunities, therefore enhancing their performance. Aven (2013) holds that risk tolerance promotes innovation as businesses are willing to try novel ideas. A company cannot implement an effective ERM program without determining and delineating its risk tolerance and appetite. The determination of organizational risk appetite is a product of debate and brainstorming sittings that involve different stakeholders. The stakeholders include executive management, external consultants, sales and marketing representatives, operations managers, and board of directors among others. Numerous metrics are used to define an organization’s risk appetite. They include leadership, ERM objectives, operations, and business strategy.
The determination of organizational risk appetite entails identifying the areas that a business is willing to allocate its scarce resources to reduce exposure. Moreover, it involves finding out the risk factors that demand prompt actions. Some risks demand a formal response plan to moderate. Thus, determining the risk appetite of a business requires understanding the threats that need a proper response and their possible material effects (Aven, 2013). Moreover, it comprises evaluating past events and how the organization handled them. Different indicators may help to determine or measure the risk appetite of an organization. They include acceptable boundaries, risk tolerance, risk portfolio views, and the difference between the apparent and real risks. Some organizations take greater risks either knowingly or unknowingly, which impact their financial performance. Hence, one of the ways of determining the risk appetite of an organization is by understanding its acceptable limits. The boundaries set the amount of risk that a business is willing to accommodate. Bromiley, McShane, Nair, and Rustambekov (2015) recommend that the management must communicate and insist on the set limits to ensure that an organization does not run into unmanageable losses.
Information about the threat tolerance of an organization is valuable in determining the risk appetite of a business. Bromiley et al. (2015) define risk tolerance as “the amount of uncertainty that an organization is willing to accept in total or more narrowly within a certain business unit, a particular risk category or for a specific initiative” (p. 267). Risk tolerance outlines the lowest and highest amount of financial resources that an enterprise is ready to lose. Such information is helpful in determining the level of risk that an enterprise can bear. As per Bromiley et al. (2015), some organizations have different categories of risk that are based on their business units. Others set risk boundaries depending on the whole organization.
An analysis of risk portfolio views of an organization helps to determine its appetite. Information regarding the risk categories of an enterprise assists in understanding its general position. Moreover, one can establish if a business has taken adequate risk to sustain itself. In some instances, organizations are beleaguered with the possibility of handling vast amounts of risks that might arise. Some threats may be apparent and others factual. Bromiley et al. (2015) aver that information about an organization’s supposed and concrete risks is helpful in determining the risk appetite of the business. It enables one to understand the hazards that an organization predicts, the measures it has taken, and its opinion about them.
Risk Assessment
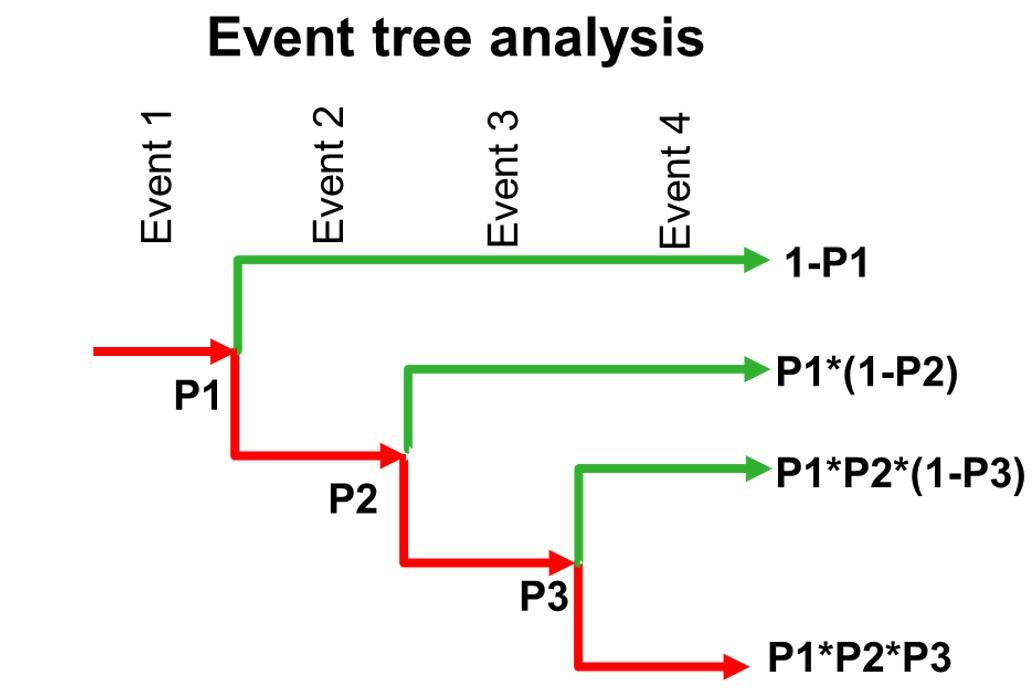
Risk assessment refers to “a process that determines the probability of losses by analyzing potential hazards and evaluating conditions of vulnerability, which could pose a threat or harm to an organization or employees” (Torabi, Giahi, & Sahebjamnia, 2016, p. 205). It entails three steps, which are identification, analysis, and evaluation. Numerous methods of risk assessment can be used to determine the probability of a dangerous event happening. They include the risk matrix approach and the event-tree method. The event-tree approach is an effective method of assessing the likelihood of a risk occurring. It is useful in a situation where the occurrence of one risk results in the rise of other successive hazards. Torabi et al. (2016) refer to such phenomenon as concatenated risks or domino effects. The dangers attributed to domino effects are difficult to evaluate and require the application of the event-tree assessment method. The technique enables one to examine all the permutations of the factors that influence the risks under review. It uses nodes to show the correlation between the evaluated incidents. According to Torabi et al. (2016), the nodes give information about all the potential states of the hazards. Individual states (branches) of the event tree provide information about the probability of a given risk happening. The diagram below represents a graphic illustration of an event-tree analysis.
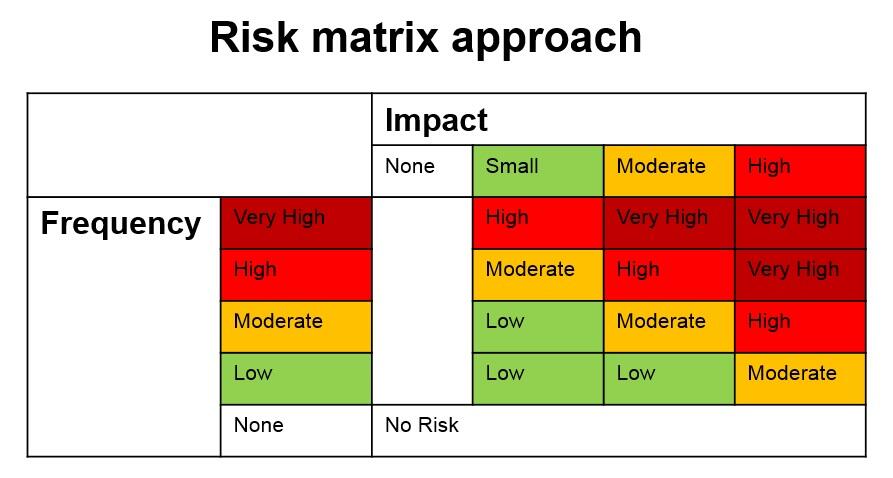
Some risk assessments are composite and challenging to conduct using numerical approaches. In some cases, the features of organizational risk are hard to quantify and quite vague. Such hazards are evaluated using the risk matrix approach. The assessment method constitutes “diagrams with consequence and frequency classes on the axes” (Torabi et al., 2016, p. 211). They enable one to classify risks without using quantitative data. The matrix comprises classes of the frequency of the dangerous incidents on one axis and their possible impacts on the other. The assessment method is useful because it facilitates the inclusion of expert opinion. Additionally, it allows the organizational leadership to see the potential impacts of specific risks, thus prompting it to take the necessary steps. Below is a diagram of the risk matrix approach.
Conclusion
Risk appetite is the measure of adverse impacts or threats that an organization is willing to accommodate. It is imperative to consider factors like acceptable boundaries, the difference between apparent and real threats, and portfolio views to understand the risk appetite of an organization. The aspects of some of the risks that affect organizations are difficult to quantify. Additionally, uncertainties attributed to some dangers make the hazards hard to evaluate. Organizations can use event-tree and risk matrix approaches to assessing potential hazards. The two assessment methods enable organizational leaders to understand the potential impacts of the given risks.
References
Aven, T. (2013). On the meaning and use of the risk appetite concept. Risk Analysis: An International Journal, 33(3), 462-468.
Bromiley, P., McShane, M., Nair, A., & Rustambekov, E. (2015). Enterprise risk management: Review, critique, and research directions. Long Range Planning, 48(4), 265-276.
Torabi, S., Giahi, R., & Sahebjamnia, N. (2016). An enhanced risk assessment framework for business continuity management systems. Safety Science, 89(1), 201-218.