Introduction
The term data refers to a collection of facts about anything. As it is often said, processed data results to information and he who has information has power. In the modern world, companies are in dire need of faster data processing in order to meet the challenges brought about by stiff competition. Managers need to obtain information fast in order to enhance their critical decisions making whose outcome highly determine the firms’ operations. Most of us undertake our daily work without having a thought of what will happen when we lose our data. We only wish that something could be done after our data is already compromised. Bearing in mind how important and critical data is to an organization there is need to do whatever it takes to guard and protect it from damage and loss. At the present information age data is stored electronically usually using flash disks, hard drives, discs, tapes etc. In this paper we analyze the problems of data loss by companies and recommend ways in which it can be reduced.
The criticality of lost data depends on its application within an organization. Study shows that when a company experiences a computer outage for more than 10 days, its chances of recovering financially are minimal and 50 percent of firms suffering that problem will experience losses for duration of five years. For example the loss of computer code presents a very significant loss, but why? This is due to the fact that it takes a lot of time and very highly skilled personnel to come up with the code. In contrast the loss of client history from the database is less significant, having the assumption that copies of the information are present. In such an occurrence a less skilled and moderately paid personnel should be able to key in the data back.
Causes of Data Loss
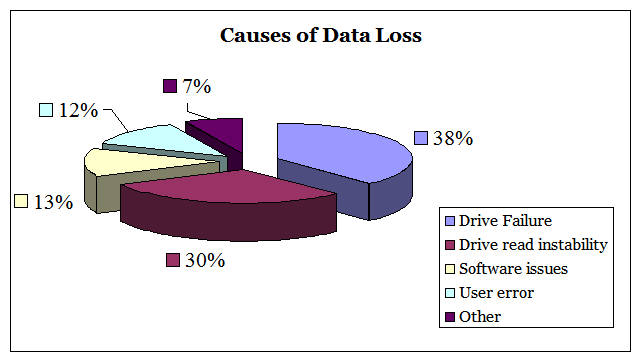
The failure of the hard drive is a common phenomenon in the current business setting. This failure can be because of software corruption, human error or other causes leading to incidents of data loss which in turn has serious consequences to a business entity. For example if a sales and marketing company experiences data loss and computer downtime, sales margin will be cut down in addition to reduced customer service while the data is being restored or rebuilt. According to a survey carried out by Verio on data loss in small business, it came out that seventy percent of the business will be critically hit financially (Verio, 2007). Even though manufacturers of hard drive allege less than 1 percent failure rate, a research carried out recently by computer scientists at Mellon University came with the findings that a 2 – 4 percent failure rate of failure is frequent and in some situations failure rate may get to 13 percent (Schroeder & Gibson, 2007). Survey that comes from companies whose specialization is data recovery attributes that 38 percent is due to hard drive failure. 30 percent is due to write, read instability. This is because of the degradation of the media. Software corruption contributes to 13 percent of another cause of data loss. This can be because of system software or another program e.g. virus attack. 12 percent of data loss is attributed to human error. This is due to incorrect partitioning of the hard drive or accidental deletion. The comparative magnitude of types of data loss is shown in the figure below.
Another cause of data loss is theft of a laptop, desktop or a storage device. The most critical issue with this kind of loss is information leakage to wrong hands. The information obtained can be used in credit cards scam hence jeopardizing customer loyalty. A permanent loss of data occurs when there is no backup for stolen data.
Effects of Data Loss
Any kind of data loss has severe implications on a company even though the impact cannot be the same due to the criticality of the lost data. Let us take an example of a research and development company; in case such a company suffers a hard disk crash the presence of confidential data on latest inventions will make the company loss trust on the current data recovery company if unable to recover the data. This poses a challenge to the company to choose a data recovery company that has lots of success in doing recovery for decades. Many R&D projects take a long period to be completed, so loosing project information implies loss of money and time spent by developers. Take another case of financial institutions running a million of transactions every day. Suppose someone wants to invest $ 3000 in stock market is unable to do so due to problems of data loss at the brokerage company. If the assumption is that the brokerage company deals with 200 transactions daily the loss will total to $ 6000 per day up to when data recovery is done successfully (Toiga, 2004).
Proved from the examples stated above loss of data can affect an organization in several ways depending on the works the company undertakes and type of information in possession. This makes choice of a data recovery software or data recovery companies very relevant.
Recommended ways of Reducing Data Loss
In cases of stolen data, forensic experts need to be called to prevent cyber criminals in their operations from causing too much damage on the customers. Too many workstations having such important information are either stolen from business premises or on transit. Unfortunately many companies will not be able to survive loss of data because of lack of proper backup policy. If a computer storing such sensitive information is stolen we consider that a permanent loss (Harris, 2007).
In case an organization is experiencing data breaches, inform all your customers about the problem without fear, this is to prevent loss of loyalty from their part. Tell them about the breach personally and possible safeguards via emails or telephone.
Business managers need to invest in technologies which can reduce the likelihood of data loss. Examples include use of computer back-up systems and virus software a. Personal Computers ought to be secured by use of password to decrease the chances of losing data to an impending burglar. Also helping as burglary prevention are computer-tracking services that can be used as a kind of “LoJack for laptops.” Another way of avoiding loss of data is implementing a sound backup policy such as online backup, data encryption and off-site data centers. Workstations also need to be password-protected to discourage theft. With financial records make sure you keep track of all transactions and if possible inform the bank storing the records for you to lock and encrypt the data for you appropriately.
However, even with the presence of reliable protection measures, episodes of loss of data occurring are inevitable. Well laid plans to tackle such episodes will lessen recovery times. Despite the fact that back-up protocols are widespread for data located in the servers; strategies to guard data in a distributed systems environment are less common. The cost of recovering data cannot be compared to the cost of its permanent loss because of the availability of technologies (Patterson, 2004).
One of the ways in which to reduce data loss by companies is by educating the employees about the importance of data to an organization and the effects of its loss. Ways and procedures to prevent loss of data should be availed to the employees. Secondly, some companies such as Symantec suggests “locking down” mobile devices, computers and other removable devices. This can be achieved by either using physical locks or software. The major problem here is how to prevent employees from taking companies internal data to the outside. Thirdly, access controls should be implemented where an individual has access to the information that he or she only requires. This implies that network access controls should be rolled out in the most appropriate way possible. Finally, data should be monitored to prevent leakages (Smith 2003).
Conclusion
Safeguarding data is a constant effort by many companies. This data is protected with the maximum efforts available. However, despite the efforts, loss of data may occur and this is the reason why companies dealing with data recovery are continually on demand. Failure of storage devices in every firm is inevitable, the question is how prepared are we to tackle such an eventuality? If the strategies discussed in this paper are employed, impact of data loss will be reduced and companies will take full advantage of the decreasing cost of storage devices.
References
- Harris, R. (2007) How Data Gets Lost, Addison Wesley: New York.
- Patterson, J 2004, A Simple Way to Estimate the Cost of Downtime, Yourdon Press: New York
- Schroeder & Gibson 2007, Disk failures in the Real world, Addison Wesley, New York.
- Smith, D 2003, Cost of Lost Data, Carswell: Toronto.
- Toiga, J 2004, Disaster Recovery Planning: Managing Risk and Catastrophe in Information Systems, Yourdon Press: New York.
- Verio, L 2007, Data Storage management Solutions, Macmillan: Toronto.